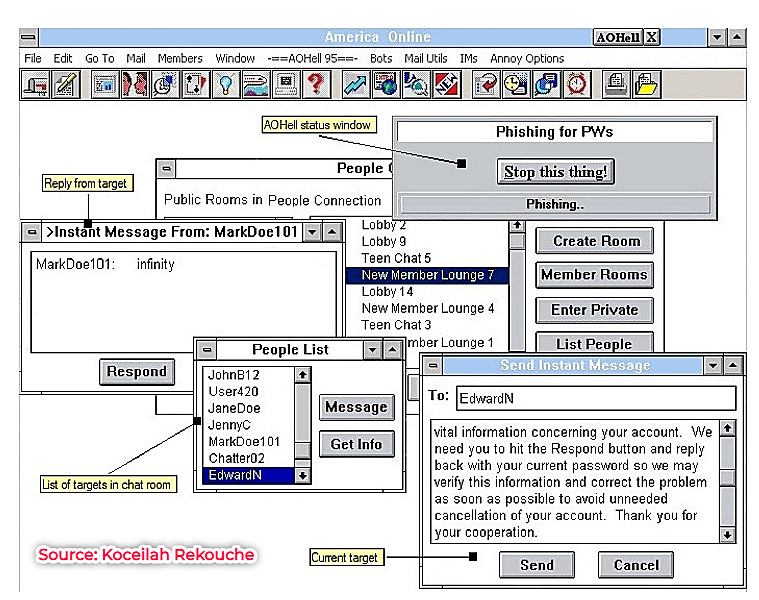
Phishing for information, Part 1: Origin and evolution | ManageEngine Expert Talks | Attack detection

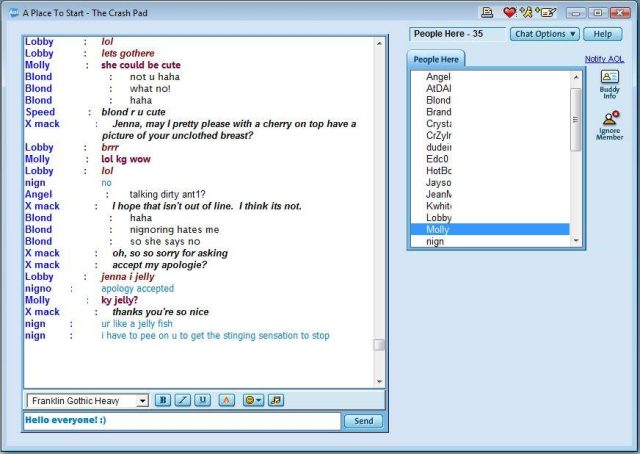
Curious about Omegle? Here's how the roulette-style chat platform can threaten your online privacy and security
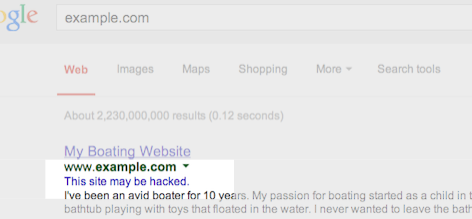
3 tips to find hacking on your site, and ways to prevent and fix it | Google Search Central Blog | Google Developers




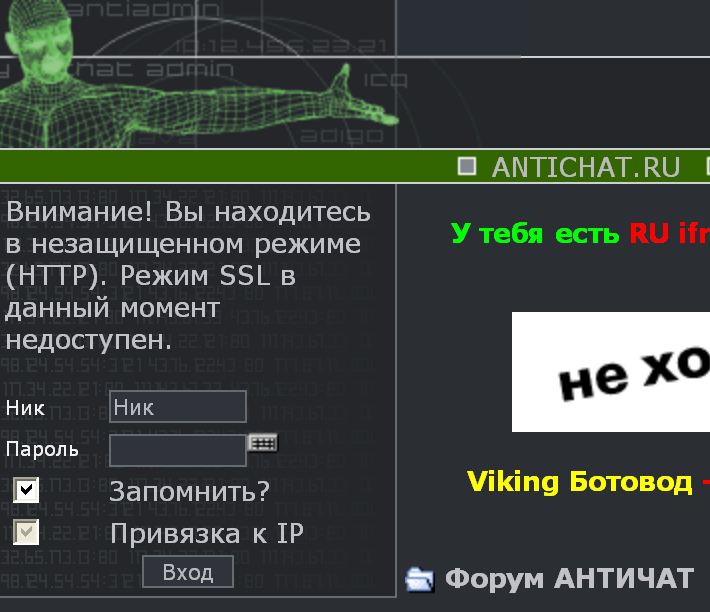





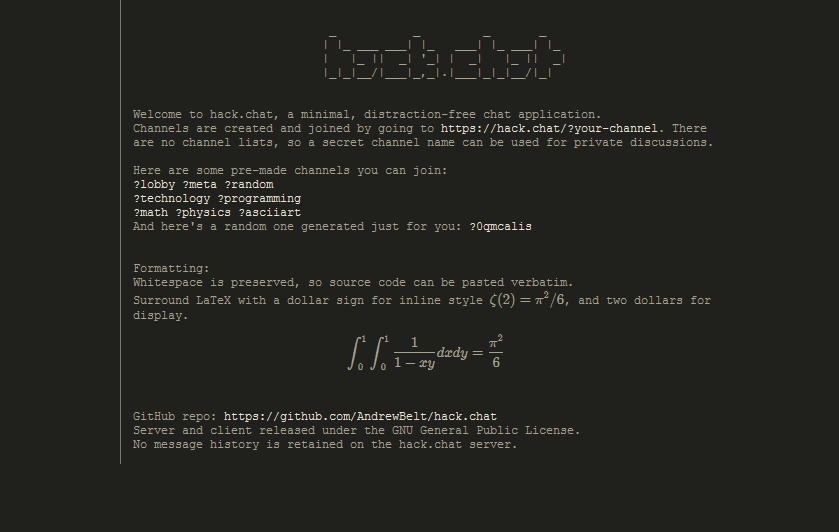
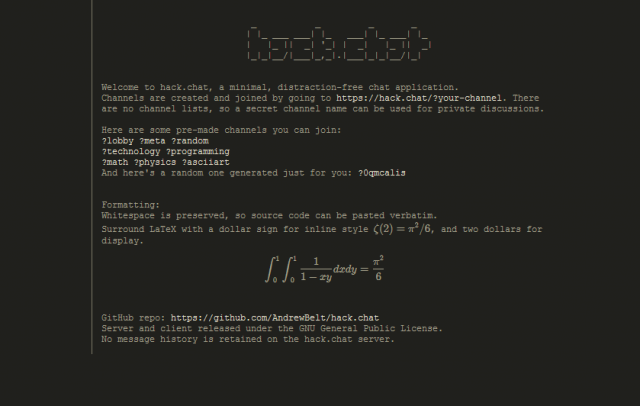
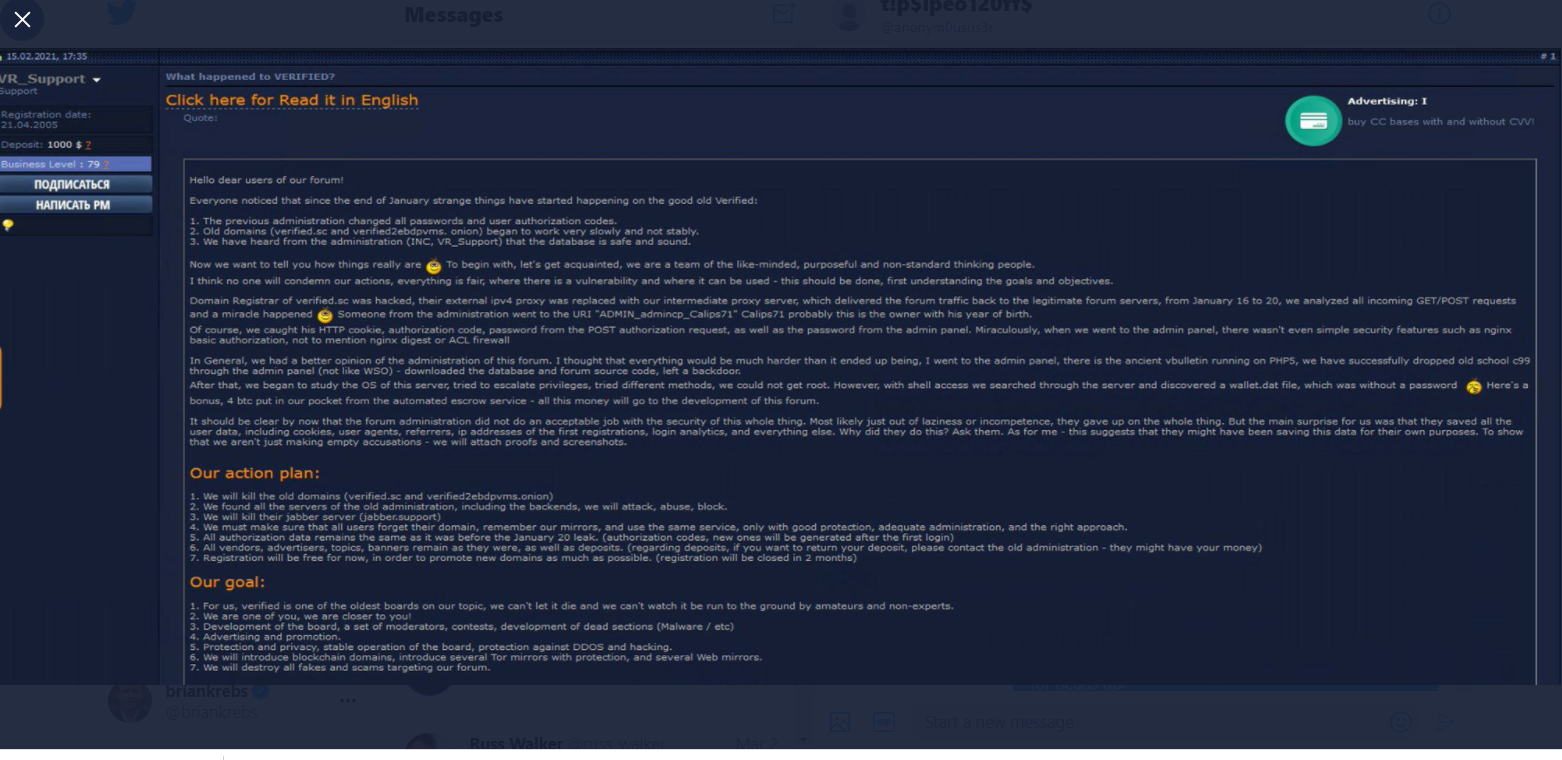
![Hacking communities in the deep web [updated 2021] | Infosec Resources Hacking communities in the deep web [updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/051415_1203_Hackingcomm3.png)