Correspondence between cellular automata and cryptography according to... | Download Scientific Diagram

de Gruyter Textbook: Discrete Algebraic Methods : Arithmetic, Cryptography, Automata and Groups (Paperback) - Walmart.com
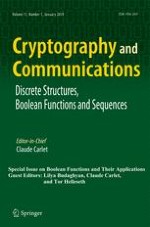
Cryptography with Advanced Functionality - Research - Advanced Cryptography Research Team | Cyber Physical Security Research Center - AIST

Cryptography, Automata and Learning Theory: Thomas, D. Gnanaraj, Jeyanthi, P. Abisha: 9788184870497: Books - Amazon.ca
Single-Share Password-Protected Visual Cryptography via Cellular Automata - Wolfram Demonstrations Project

PDF) Generating PNS for Secret Key Cryptography Using Cellular Automaton | Amiya Rath - Academia.edu

A Novel Image Encryption Scheme Based on Reversible Cellular Automata and Chaos (@ijitcs) - Readera.org

Amazon | Theoretical Computer Science: Introduction to Automata, Computability, Complexity, Algorithmics, Randomization, Communication, and Cryptography (Texts in Theoretical Computer Science. An EATCS Series) | Hromkovič, Juraj | Cryptography

Application of Linear and Non Linear Modified 3D Cellular Automata Rules in Cryptography for Improved Security of Transmitted Data | Scientific.Net




![PDF] Cellular Automata and Cryptography | Semantic Scholar PDF] Cellular Automata and Cryptography | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/513f8c667fa015879356692c3e98f4fb8d052303/30-Figure2.7-1.png)


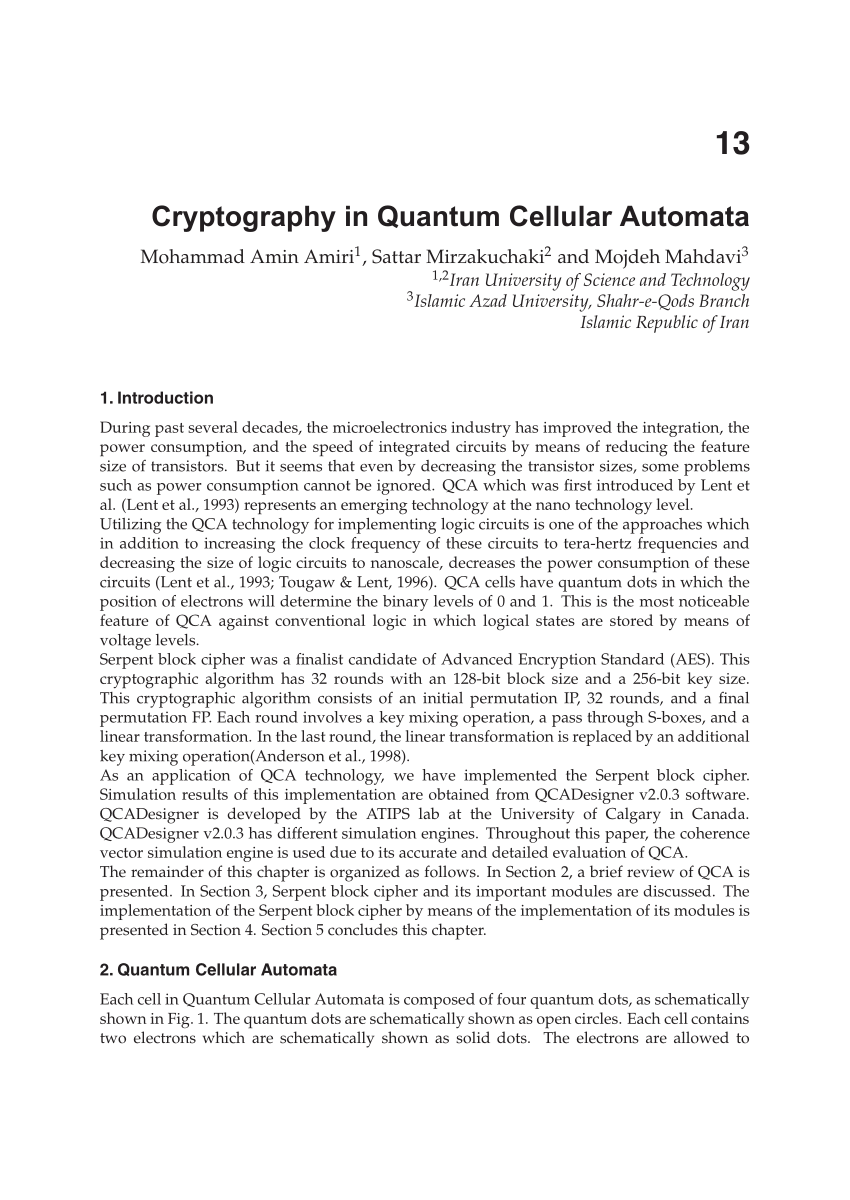
![PDF] Evolving collective behavior of cellular automata for cryptography | Semantic Scholar PDF] Evolving collective behavior of cellular automata for cryptography | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a63484c2d43816be29a312cae88395bba314e435/2-Figure1-1.png)